Wasabi Protocol $5M drain linked to single deployer key
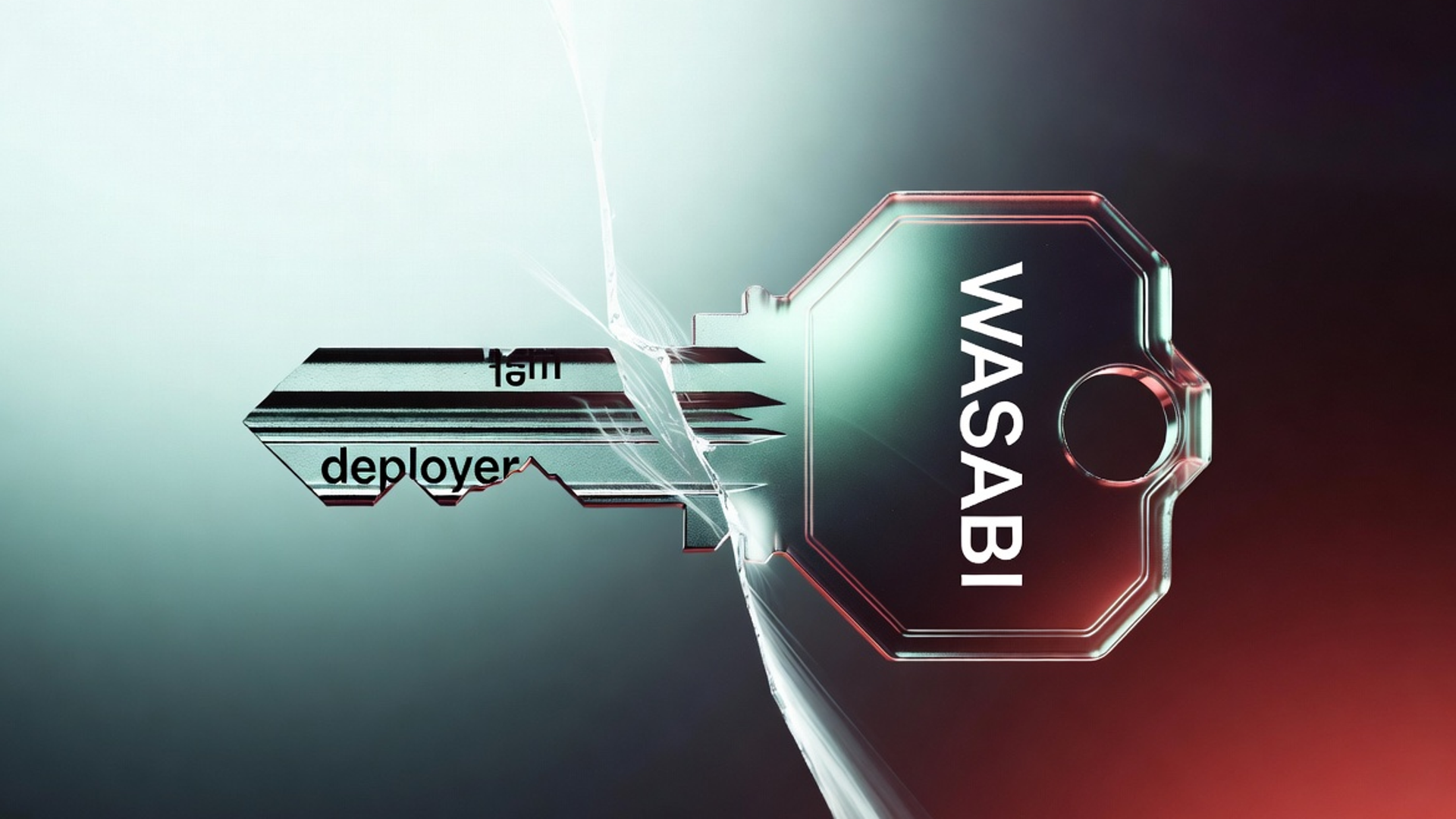
An attacker used Wasabi’s deployer admin key to upgrade vaults and the LongPool to a malicious implementation, draining about $5 million across four chains.
On-chain security firms Blockaid and PeckShield report that an attacker used Wasabi Protocol’s deployer admin key to upgrade perpetual vaults and the LongPool to a malicious implementation, extracting roughly $4.55 million according to Blockaid and more than $5 million by PeckShield’s tally. Funds were taken across Ethereum, Base, Berachain and Blast. Affected vault and pool share tokens have been flagged as compromised and their redemption value is reported near zero.
Investigators traced control of the ADMIN_ROLE to a single externally owned address, wasabideployer.eth, which held the role for Wasabi’s PerpManager AccessManager. On-chain analysis shows the attacker called grantRole on that deployer wallet with zero delay, immediately granting an orchestrator contract admin privileges. The newly authorized admin then executed a UUPS upgrade that replaced vault and LongPool logic with code that siphoned balances.
Wasabi Protocol posted a notice to users: “We’re aware of an issue and are actively investigating. As a precaution, please do not interact with Wasabi contracts until further notice.”
The incident follows several DeFi losses reported in the same period, including a drain at a token project later identified as a foundation recovery, a bridge loss on Base that moved tokens to Ethereum, and a perpetuals protocol that paused after losing roughly $1.14 million in USDC. Security teams and on-chain trackers are noting the concentration of rapid incidents while totals are updated.
On-chain investigators flagged the technical pattern as a single-key admin that can perform immediate upgrades without a multisignature requirement or a timelock. Blockaid found matching orchestrator and strategy bytecode linking this breach to prior on-chain activity targeting Wasabi, indicating the attacker reused or adapted a previously successful approach.
A developer on social media proposed that a state actor could have trained an automated model on years of stolen DeFi data and that the model might now be operating as an autonomous exploiter. The developer wrote, in part, that a state-funded model could be “trained on the insane amounts of data obtained by hacking DeFi protocols over the last 10 years” and then used to find and execute flaws. Security researchers caution that the claim is unproven but say it highlights concern about the gap between attacker tools and protocol defenses.
For context, many DeFi vaults use an upgradeable proxy pattern that separates user funds in storage from logic in an implementation contract. When an address with admin privileges calls the upgrade function, the proxy begins using new implementation code. If an attacker controls that admin key, they can point the proxy at code that withdraws or redirects funds. In this case, the UUPS upgrade pattern was used to swap in a malicious implementation that drained vault balances.
Wasabi and other teams are continuing on-chain forensic analysis while community trackers attempt to trace proceeds. The deployer key remained active at the time of reporting and investigators and security firms are updating loss totals as more chain data is analyzed.









