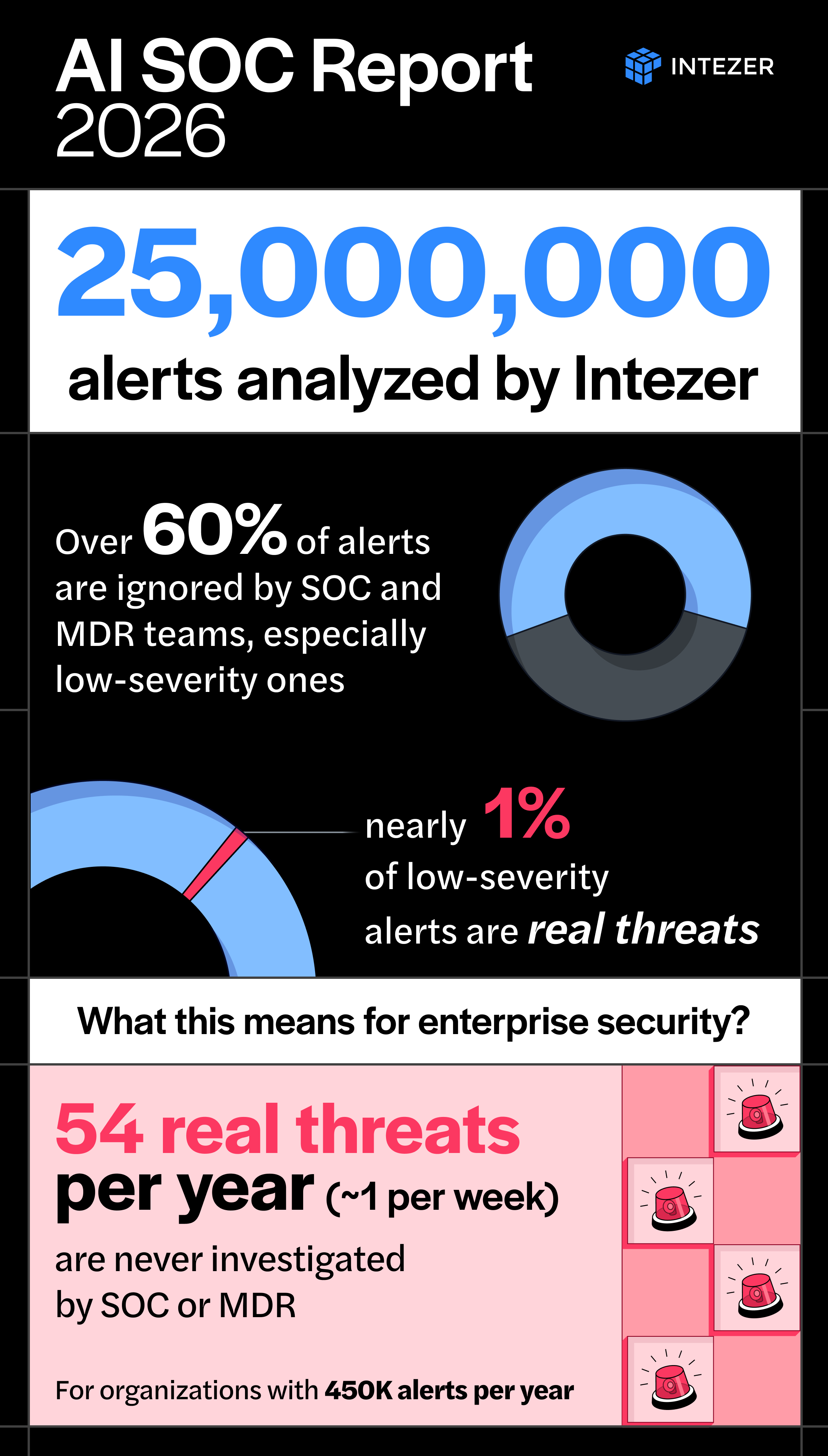
Enterprises miss one threat a week from low-severity alerts

Analysis of 25 million alerts found nearly 1% of confirmed incidents began as low‑severity or informational alerts, about one missed threat per organization each week.
A 2026 analysis of 25 million enterprise security alerts found nearly 1% of confirmed incidents originated from alerts initially labeled low‑severity or informational, a rate that rises to about 2% on endpoints. At typical enterprise scale, the report says, that equals roughly one real threat missed per week per organization.
The dataset behind the findings included telemetry from 10 million monitored endpoints and identities, 82,000 forensic endpoint investigations that included live memory scans, analysis of 180 million files, data from 7 million IP addresses and 3 million domains and URLs, and more than 550,000 phishing emails.
Endpoint investigations identified 2,600 active infections among the 82,000 memory scans. The report notes that 51% of those confirmed compromised endpoints had been marked “mitigated” by the endpoint detection and response tool before forensic memory analysis detected active malware. Memory scans found active families including Mimikatz, Cobalt Strike, Meterpreter and StrelaStealer running in memory after EDR had closed the ticket.
Phishing telemetry showed fewer than 6% of confirmed malicious messages contained attachments; most relied on links and social engineering. Attackers hosted malicious pages on services that receive default trust, including Vercel, CodePen, OneDrive and PayPal’s invoicing system. The report identifies four techniques used at scale to evade email gateways: Base64 payloads embedded in SVG images, links hidden in PDF annotation metadata, dynamically loaded phishing pages delivered through legitimate OneDrive shares, and DOCX files that conceal archived HTML content with embedded QR codes. The analysis also notes a correlation where pages using Cloudflare Turnstile CAPTCHA were more likely to be malicious while Google reCAPTCHA aligned more with legitimate content.
Cloud alert data in the report showed a concentration of defense‑evasion and persistence activity rather than noisy lateral movement or immediate privilege escalation. Common behaviors included token manipulation and abuse of legitimate cloud features. Misconfigurations in AWS, particularly S3, accounted for about 70% of cloud control violations recorded, with repeated issues in access management, server logging and cross‑account restrictions; most of these events were classified as low severity.
The report attributes missed threats to operational limits in security operations centers and managed detection and response services. It reports that roughly 60% of alerts go unreviewed, whether handled internally or outsourced, and that teams commonly automate closures and focus investigations on high‑severity items. The analysis states that adding analysts or deploying SOAR platforms changes scale but does not eliminate the investigative capacity ceiling.
To test full‑coverage investigation, the dataset was triaged and investigated using an AI SOC platform. The platform escalated fewer than 2% of alerts to human analysts, reported 98% verdict accuracy and achieved sub‑minute median triage times across the full volume. The report says providing forensic‑grade analysis to every alert surfaced early‑stage threats and produced feedback that can be used to tune detection rules.
The full findings and technical detail are published in the 2026 AI SOC Report for CISOs by Intezer.