North Korean hackers behind 76% of 2026 crypto losses

North Korean hackers tied to two April attacks accounted for 76% of crypto hack losses through April 2026, stealing about $577 million, TRM Labs reports.
North Korean-linked hacking groups were responsible for 76% of recorded crypto hack losses through April 2026 after two April attacks that together took roughly $577 million, TRM Labs reported.
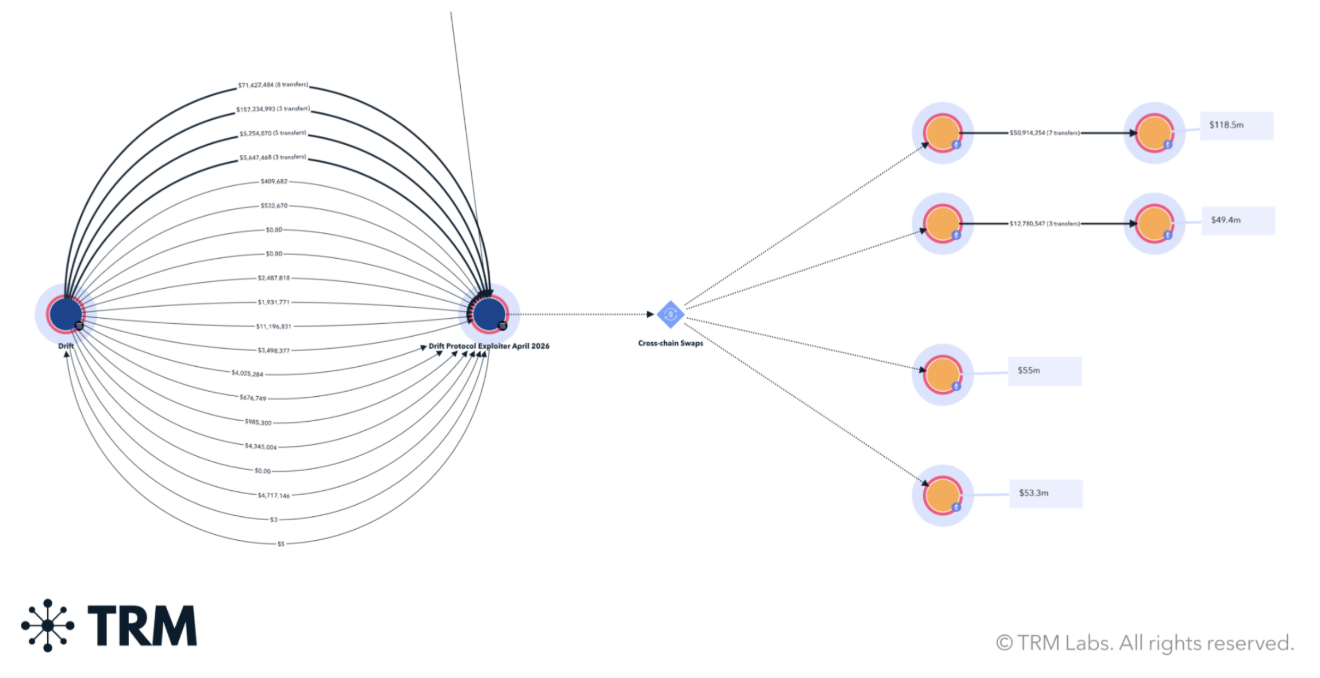
On April 1, attackers exploited Drift Protocol, a Solana-based perpetual exchange, and stole about $285 million. Drift’s follow-up incident report said the breach followed a six-month intelligence operation tied to North Korean actors. The breach affected multiple protocols that interacted with Drift and put pressure on liquidity across parts of the Solana ecosystem.
Solana yield platform Carrot announced on April 30 that it would shut down and set a May 14 deadline for users to withdraw remaining balances from Boost, Turbo and CRT positions before forced deleveraging.
On April 18, a cross-chain bridge operated by KelpDAO was drained of 116,500 rsETH, valued at about $292 million. Investigators linked the KelpDAO exploit to the Lazarus Group’s TraderTraitor cluster. The incident coincided with sharp declines in Aave’s price and a fall in total value locked across decentralized finance platforms.
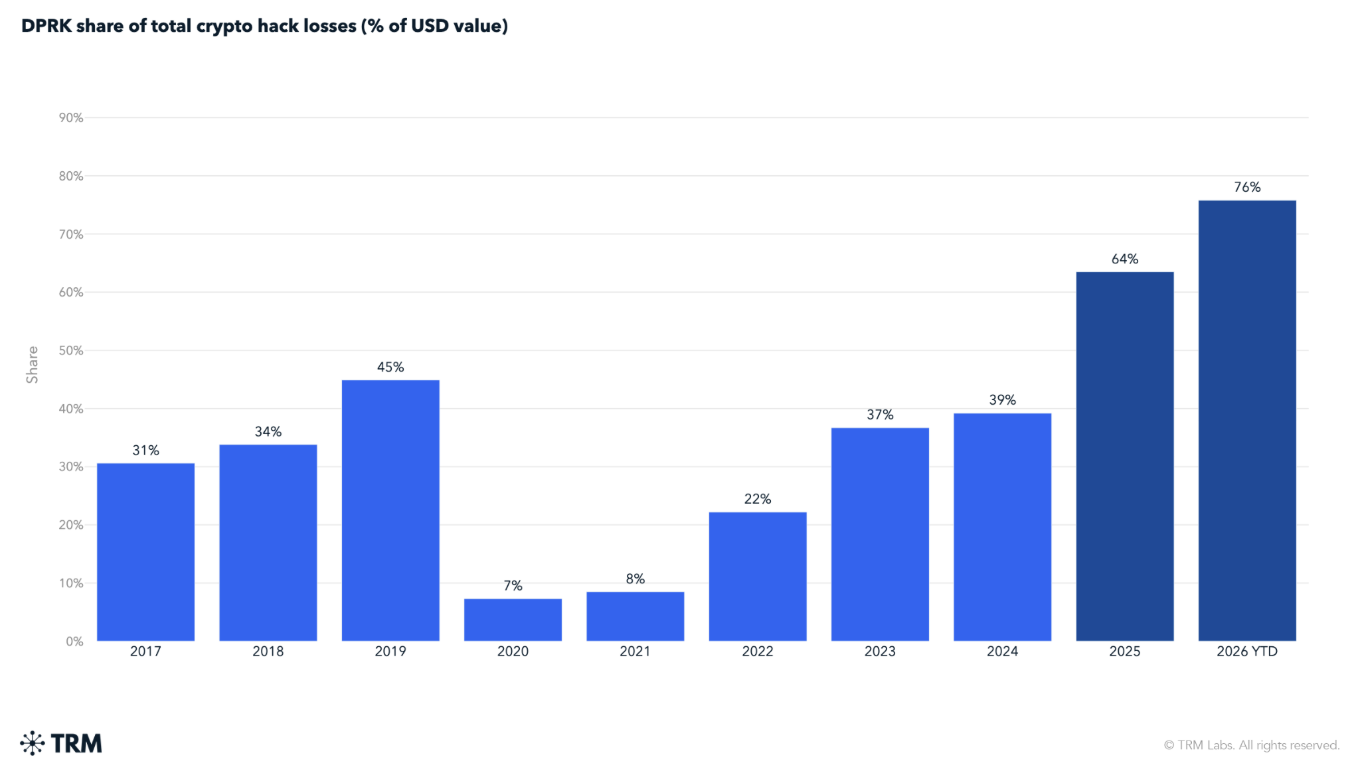
TRM’s report documents a steady rise in the share of losses attributed to North Korean groups. Their share of total hack losses was under 10% in 2020–21, rose to 22% in 2022, then to 37%, 39% and 64% in subsequent years, and reached 76% through April 2026. TRM also reported that North Korean actors drained at least $2.02 billion in digital assets during 2025.
TRM analysts wrote,
North Korean hacking groups accounted for 76% of all crypto hack losses in 2026 through April — not because North Korea launched a wave of attacks, but because two attacks totaling USD 577 million dwarfed everything else.
The report noted that attack frequency has not increased; instead, the groups are carrying out a small number of highly targeted operations each year.
TRM said its analysts are seeing higher technical sophistication in recent operations and have begun to speculate that North Korean teams may be using artificial intelligence tools to aid reconnaissance and social engineering. The report links the Drift attack to weeks of targeted manipulation of complex blockchain mechanisms rather than simple private key compromises.
Investigations into both incidents are ongoing. Drift and KelpDAO have published technical and incident reports, and law enforcement and blockchain security firms are tracing funds and analyzing attacker infrastructure. Affected protocol teams have responded with shutdowns, emergency withdrawals and updated risk assessments.