2026 IoT botnets fuel record 15.72 Tbps DDoS attack

IoT botnets in 2026 launched a 15.72 Tbps DDoS on Microsoft Azure and infected millions of routers, cameras and smart devices to run DDoS and proxy services.
IoT botnets in 2026 continued to compromise millions of connected devices and launched a cloud DDoS that peaked at 15.72 Tbps and 3.64 billion packets per second. Security researchers traced that cloud attack to the Aisuru botnet and to a single edge device in Australia.
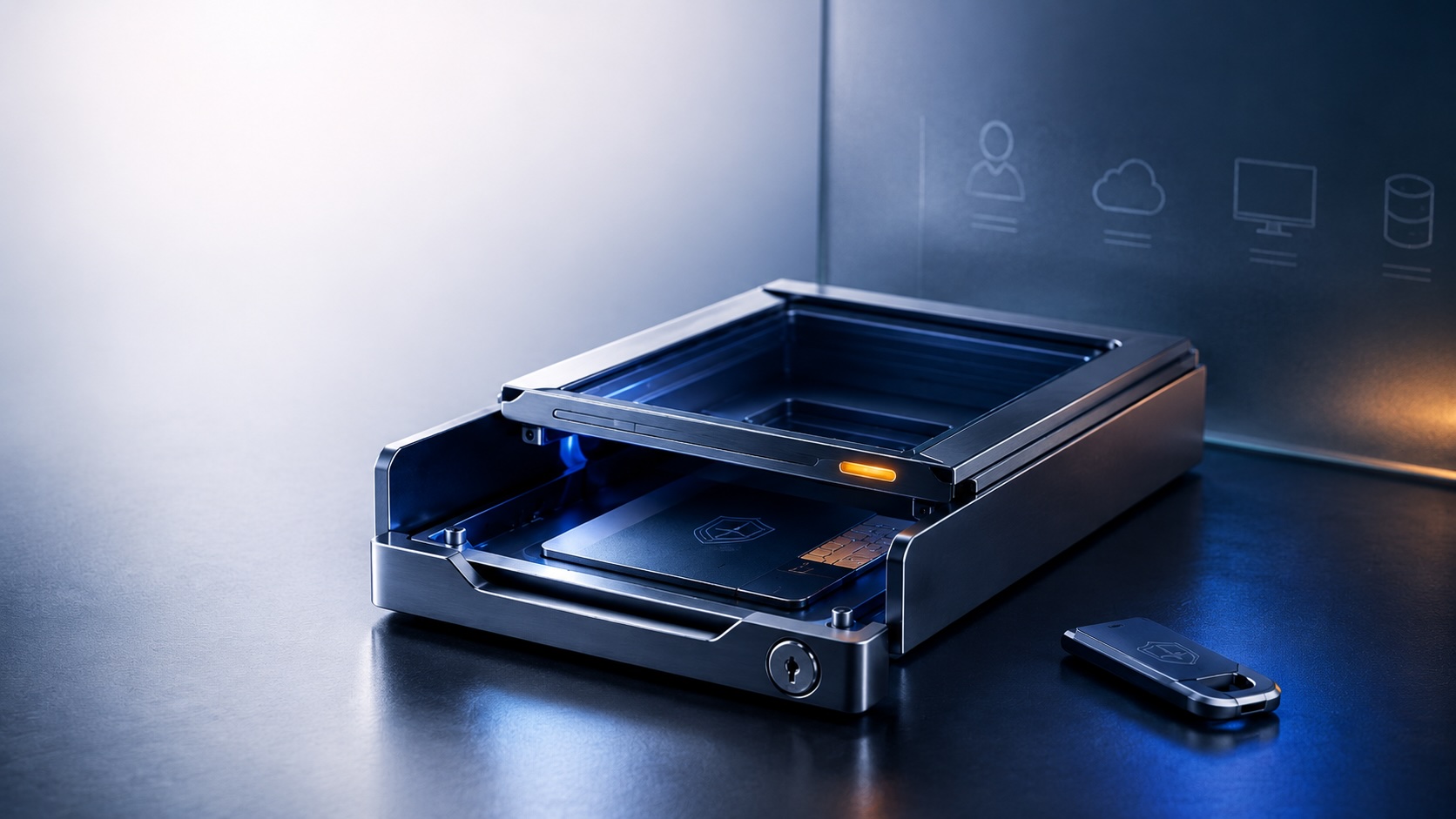
Aisuru and related strains exploited flaws in home routers and surveillance cameras to scale distributed denial-of-service attacks and to provide proxy services that mask attackers’ traffic. Operators enrolled exposed edge devices to relay and anonymize other campaigns.
In January, a Linux botnet called RondoDox exploited a remote code execution vulnerability in HPE OneView and carried out more than 40,000 automated attacks targeting government, financial and industrial systems. The U.S. Cybersecurity and Infrastructure Security Agency added the HPE OneView flaw to its list of known exploited vulnerabilities. Analysis of the RondoDox activity found much of the traffic originated from a single Dutch IP address; the United States recorded the largest number of attack attempts, followed by Australia, France, Germany and Austria.
An Android variant linked to Aisuru, known as Kimwolf, grew to more than two million infected hosts by January. Most Kimwolf infections began through weak residential proxy setups that exposed devices on internal networks. Researchers observed Android TVs and streaming devices with exposed Android Debug Bridge services among frequent targets.
In March, threat researchers flagged a new strain named KadNap that infected over 14,000 edge devices, primarily Asus routers. KadNap incorporated those devices into the Doppelgänger proxy service to support anonymous DDoS campaigns.
Law enforcement in the United States, Germany and Canada coordinated actions against a cluster of botnets that included Aisuru, Kimwolf, JackSkid and Mossad. Authorities estimated the combined networks had infected more than three million devices worldwide.
Following the outbreak of fighting between the United States and Iran, researchers reported increased targeting of internet-connected surveillance cameras in Israel, other Middle Eastern countries and Cyprus.
One vendor report stated:
Starting February 28, we observed a spike in targeting of IP cameras in several countries in the Middle East including Israel, UAE, Qatar, Bahrain, Kuwait and Lebanon, while also similar activity occurred against Cyprus. The attack infrastructure we track combines specific commercial VPN exit nodes (Mullvad, ProtonVPN, Surfshark and NordVPN) and virtual private servers (VPS), and is assessed to be employed by multiple Iran-nexus actors.
Security recommendations for organizations include enforcing device authentication, encrypting traffic, applying DNS filtering, regularly patching software and firmware, disabling non-essential services, segregating IoT devices on separate networks and using unique, strong passwords for each device.
Researchers point to the large number of connected devices, frequent weak configurations and gaps in routine maintenance as factors that allow attackers to recruit endpoints for DDoS and proxy services.