European MSPs must close SaaS sovereignty gap

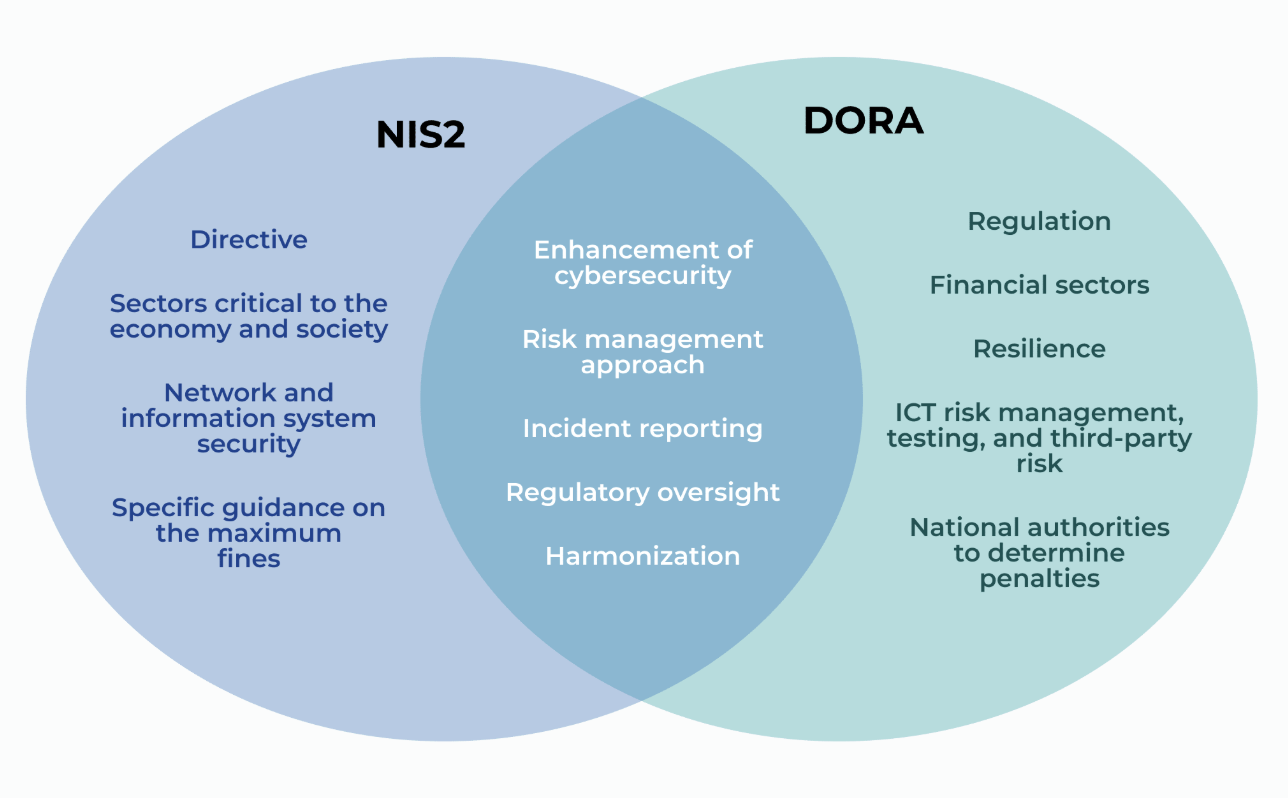
Under DORA and NIS2, EU MSPs must treat data sovereignty as an operational duty; customers now demand proof of SaaS data control and recoverability.
Under EU rules DORA and NIS2, managed service providers across Europe are being required to treat data sovereignty as an operational responsibility. Customers now expect evidence that SaaS data can be controlled and recovered, not only information about where it is stored.
Regulatory pressure and customer due diligence have shifted questions from location to control. Buyers and auditors are asking who can access data, how quickly it can be restored and whether recovery processes meet regulatory requirements. These questions fall to MSPs that manage SaaS applications, backups and critical data environments.
Operational sovereignty is being described as a capability issue. Providers must demonstrate that data can be accessed and restored when platform access is blocked by a cyber incident, outage or misconfiguration. Historic MSP offerings emphasized uptime, capacity and cost efficiency; current requirements focus on recoverability within defined timeframes and under real-world conditions.
The Keepit Annual Data Report 2026 provides operational detail. The report found about 90% of restore actions are single-file recoveries and that most restore activity takes place during working hours. The report also identified a maturity gap by organization size: 28% of small and medium businesses perform restores regularly, compared with 91% of commercial organizations and 95% of enterprise organizations. The report noted that major outages did not produce a measurable increase in routine restore testing.
The broader adoption of SaaS has increased recovery complexity. Many organizations run critical functions across multiple SaaS platforms and assume those vendors provide full data protection. In practice, SaaS vendors typically guarantee availability while longer-term protection and recoverability often fall to customers or their MSPs. If a primary SaaS platform restricts access during an incident, the ability to recover data may depend on the platform’s own export and access mechanisms. Providers describe the resulting shortfall as a sovereignty gap.

Industry operators recommend changes to service design to address the gap. Practical measures include ensuring backups and recovery workflows can run independently of the primary SaaS environment, reducing reliance on single vendors, conducting regular recovery tests that reflect operational conditions, and providing customers clear visibility into recovery timelines and dependency chains.
Buyers in regulated sectors are increasingly including detailed recovery plans and documented testing in procurement checks. The regulatory and commercial requirements place a greater emphasis on demonstrable recoverability, and MSPs that supply documented, testable recovery processes are meeting those specific demands.
The Keepit report concluded, “Resilience is not theoretical; it is tested daily in small but critical ways,” highlighting the frequency and practical nature of recovery activity in everyday operations.








