One in four firms expose MySQL as AI speeds exploits

Intruder’s 2026 Attack Surface Management Index found 25% of organizations have MySQL databases exposed online, while advances in AI are shortening exploit timelines.
Security firm Intruder published its 2026 Attack Surface Management Index, finding one in four organizations had MySQL databases reachable from the public internet. The report also tied a shrinking window between vulnerability discovery and exploitation to advances in autonomous AI models.
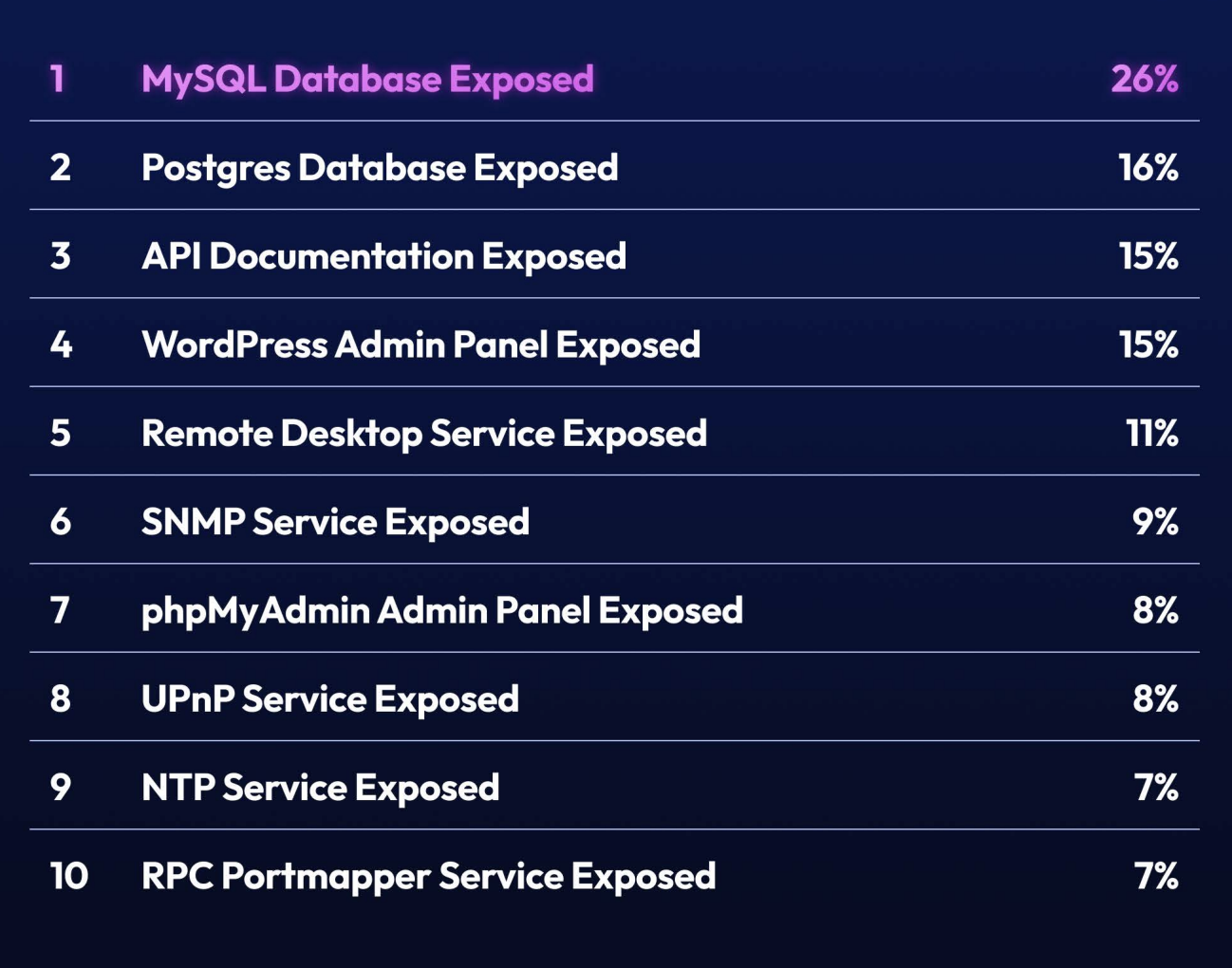
The index measured internet-facing issues across HTTP panels, open ports and services, databases, and exposed files and information. It found 25% of organizations had MySQL instances publicly reachable and 16% had exposed Postgres databases. Exposed API documentation affected more than one in seven organizations, outstripping remote desktop protocol services that remain a common ransomware entry point.

Nearly half of organizations had risky open ports and services. Remote Desktop Protocol was the most frequently exposed service. The report found WordPress admin interfaces were internet-facing in 15% of cases and phpMyAdmin in 8% – both tools typically intended for internal use. Legacy network services such as SNMP and UPnP appeared on the public internet in 9% and 8% of organizations respectively.
Intruder flagged exposed databases as attractive targets for threat actors, particularly ransomware groups, because they often contain sensitive data. Chris Wallis, Intruder’s CEO and founder, warned many of the exposures do not require a software flaw to be exploited and pointed to credential stuffing and brute-force attacks as common methods. He said, “Many of the exposures we examined don’t even need a CVE to be exploited. For example, an exposed database or admin panel can be compromised through brute force or credential stuffing alone.”
The report documented wide variation in how quickly organizations fix exposed systems. Midmarket firms took the longest to remediate, averaging 56 days to close security gaps-nearly four times slower than smaller enterprises. Banks and retailers were among the fastest, resolving exposures in about 11 and 10 days respectively, while insurance and pharmaceutical companies averaged more than 40 days.
Intruder linked faster exploitation to high-capacity autonomous AI models that automate reconnaissance and parts of attack workflows. Wallis added the security industry is seeing “a major compression in the time between vulnerability discovery and exploitation” and warned remediation windows “are open far too long.” The report urged organizations to reduce internet-facing exposure of admin panels, databases and private APIs and to speed patching and configuration management to limit risk.








