15 agencies: China-linked actors use home-device botnets
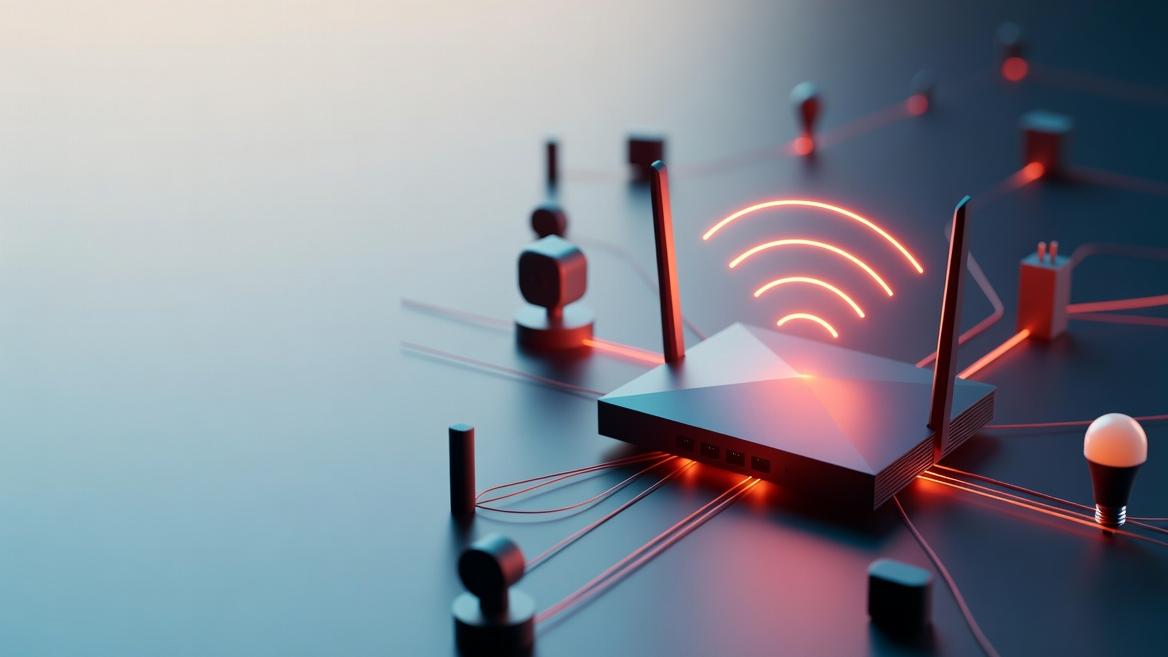
UK NCSC and 15 international partners warn China-linked groups route attacks through botnets of compromised home and SOHO routers and smart devices to obscure the origin of malicious traffic.
The UK’s National Cyber Security Centre and 15 international partners issued a joint advisory warning that China-linked threat actors are routing scans, malware deliveries and data theft through botnets made from compromised home routers, small-office routers and consumer smart devices.
The advisory describes a shift from attackers using dedicated servers to relaying malicious traffic through hundreds of thousands of everyday internet-connected devices. The document links this pattern to campaigns associated with groups tracked as Volt Typhoon and Flax Typhoon.
The NCSC identified a covert network called Raptor Train that infected more than 200,000 devices worldwide in 2024. The FBI has linked the botnet’s management to Integrity Technology Group, a Beijing-based company that the UK sanctioned in December 2025. The advisory also names a KV Botnet used by Volt Typhoon to establish footholds on critical infrastructure. U.S. Department of Justice filings cited by the advisory reference compromises affecting energy grids, transport systems and government networks in the United States and allied countries.
Many hijacked devices are end-of-life webcams, digital video recorders, firewalls and network storage devices that no longer receive security patches from manufacturers. The advisory says their widespread availability makes bulk exploitation straightforward and causes malicious traffic to appear to come from ordinary home addresses.
The document flagged a problem it calls ‘indicator of compromise extinction,’ where identifiers used to track attackers disappear almost as quickly as researchers publish them. Paul Chichester, director of operations at the NCSC, warned that China-based cyber groups have shifted to using these networks to hide malicious activity and avoid accountability.
The advisory urges organisations to establish baselines for normal network traffic, adopt dynamic threat feeds and treat China-linked covert networks as advanced persistent threats. It directs defenders to monitor unusual outbound connections from SOHO devices and to harden or replace end-of-life equipment where possible.
The advisory notes that digital-asset losses tied to cyber activity exceeded $2 billion in 2024 and says the coming months will test whether defenders can keep pace with these tactics.